Operation Epic Fury vs Operation Midnight Hammer
Operation Midnight Hammer (June 22, 2025) and Operation Epic Fury (February 28, 2026) are both U.S. military operations against Iran, but they are very different in how they are set up. Midnight Hammer was a problem that involved breaking into a hardened target in one night.
Epic Fury is a campaign that lasts for several days and takes place in several areas. Its goal is to destroy Iran’s ability to coordinate, defend, and retaliate on a large scale. The difference is important because it changes everything, like force packages, targeting cycles, munitions burn rates, air defense postures, and the risk of escalation.
| Dimension | Midnight Hammer | Epic Fury |
|---|---|---|
| Core mission logic | “Hit a few, very hard” (HDBT/nuclear nodes) | “Collapse the system” (C2, IADS, missiles, maritime, enabling nodes) |
| Signature weapons | GBU-57 MOP + Tomahawk | Tomahawk, stealth bombers/fighters, EW, ISR, and one-way attack drones |
| Key enabling problem | Stealth + EMCON + tanker choreography + precise weapon–target pairing | Sustained kill-chain throughput: ISR → targeting → strike → BDA → re-attack, while defending bases |
| Main technical uncertainty | Underground BDA and displaced materials | Attrition/munitions endurance and defending a wide footprint against retaliation |
(“HDBT” = hardened and deeply buried target; “IADS” = integrated air defence system; “BDA” = battle damage assessment.)
1) Midnight Hammer: HDBT Penetration
Targets Dictated the Engineering
According to public reports and US briefings, Midnight Hammer was an attack on Iran’s three main nuclear sites: Fordow, Natanz, and Isfahan. Those places, especially Fordow, are the perfect example of HDBT: important equipment buried under a lot of rock, built to withstand regular air attacks. In that case, choosing a weapon is just as much about penetration and fuzing as it is about guidance.
GBU-57 MOP: the HDBT Solution
According to a Reuters report, the U.S. calls the GBU-57 Massive Ordnance Penetrator a “30,000-lb precision weapon” that can go deep into hardened underground facilities. Reuters cites a 2012 congressional report that says it can penetrate “up to 200 feet” in some conditions. A MOP-style weapon is a kinetic penetrator in terms of education.
It stays intact through impact because of its mass, sectional density, and hardened casing. It then detonates after reaching a certain depth thanks to delayed fuzing. This delay serves as the technical pivot: premature detonation wastes energy in the open air or on rocks, while prolonged detonation risks venting energy into voids or overlooking the most valuable internal spaces.
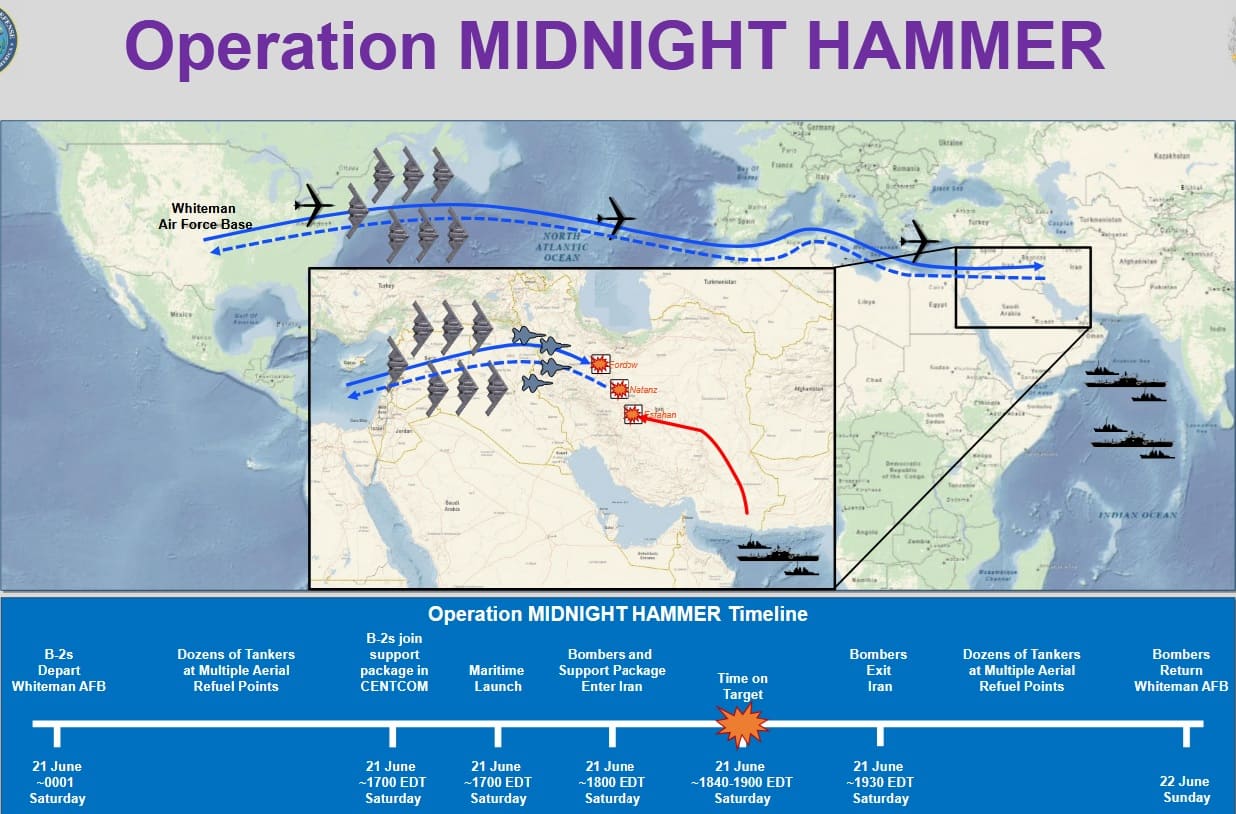
Penetration Package Design
According to Reuters, a package of seven B-2 bombers flew an 18-hour route with little communication, got fuel in the air, and had a deception element (decoy B-2 movements were seen heading toward Guam while the real strike package flew east). At the same time, a U.S. submarine fired more than two dozen Tomahawk land-attack cruise missiles. Fighters acted as decoys and sweepers.
This layout is a classic high-end raid design:
- Stealth penetrators (B-2) handle the hardest aimpoints.
- Standoff weapons like the Tomahawk can attack nodes that are on the surface or not buried very deep, making it harder to control defense.
- Deception and EMCON (emissions control) cut down on warning time and make it harder for Iran to respond.
BDA: Harder Than the Strike
When it comes to underground complexes, the simple question is, “Did we hit the coordinates?” The difficult question is, “Did we break the function?” Commercial satellite images can show holes in the ground, disturbed earth, and other effects, but they can’t easily check the state of deep hallways, cascades, power conditioning, or the remaining centrifuge inventories. Reuters cites image analysts who suggest that images alone may not provide a reliable assessment of some important halls due to their deep burial.
CFR’s first analysis made the same point: the assessments were “murky,” and it brought up the extra uncertainty of unaccounted enriched uranium stockpiles. This is important because you can destroy facilities and still have a way to rebuild if material and some equipment survive somewhere else. What you should learn from HDBT (High-Density Bombing Target) raids is that the kill mechanism is rarely just one explosion. There are many things that make it hard to quickly check: structural collapse, internal shock, fires, power loss, blocked access, and long repair times.
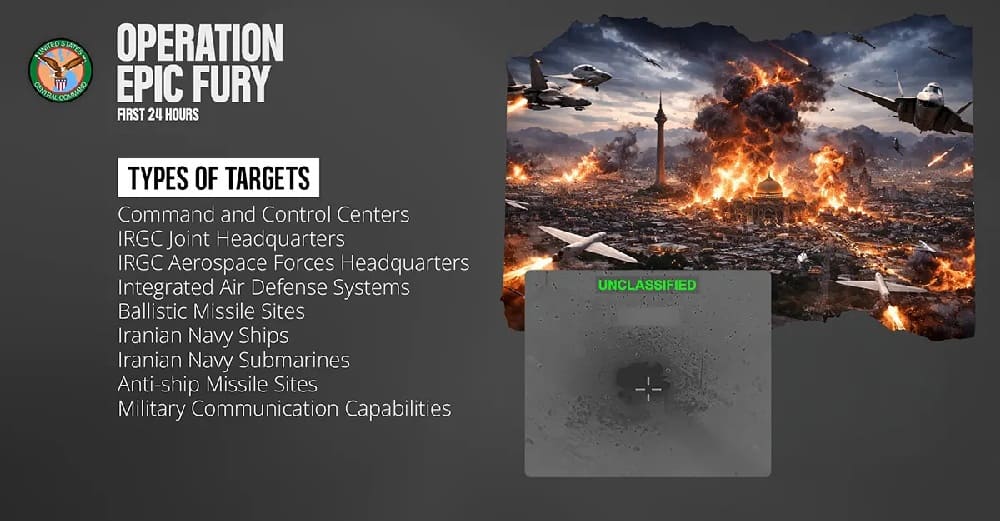
2) Epic Fury: System Disruption at Scale
In the first few hours of Epic Fury, CENTCOM’s launch statement mentions “precision munitions launched from air, land, and sea.” It also says that Task Force Scorpion Strike used low-cost one-way attack drones for the first time in combat. CENTCOM also said it was the “largest regional concentration of American military firepower in a generation.”
More Than Strike Volume
Epic Fury is more like a campaign than a raid, which means that success depends on a steady stream of kills rather than one perfect weapon-target pairing. People often call the relevant technical loop F2T2EA.
- Find (ISR detects)
- Fix (confirm location/identity)
- Track (maintain custody)
- Target (legal/ROE and weaponeering)
- Engage (deliver effects)
- Assess (BDA and re-attack decisions)
A campaign wins by running this loop faster than the opponent can hide, move, regenerate, or retaliate—and by protecting your own basing network while you do it.
Enablers: EW, ISR, C2, Connectivity
Reports from the Air & Space Forces indicate that there was significant help from public sources during Epic Fury, including the EA-18G Growler electronic attack aircraft, the E-3 AWACS and carrier E-2D for battle management, the E-11 BACN for airborne communications, ISR assets like the RC-135 Rivet Joint, P-8 Poseidon, and MQ-9 Reaper, as well as heavy tanker
Educationally, this is the “real” campaign engine:
- EW aircraft degrade radars and comms, which makes stealth and strike aircraft safer.
- AWACS/battle managers turn many shooters into one coordinated formation.
- Comms relays keep data links and voice networks alive across terrain, distance, and jamming.
- ISR aircraft provide targeting-quality data, emitter mapping, and post-strike assessment.
This is important because an IADS is not “a missile battery.” It’s a network that goes from sensors to communications to command nodes to launchers. Campaign-level suppression means breaking enough connections so that the network stops acting like a network.
LUCAS: Affordable Mass Effects
According to Reuters, the U.S. used “suicide” drones that look like LUCAS (Low-Cost Unmanned Combat Attack System), and CENTCOM used one-way drones based on Iran’s Shahed design. The December 2025 release from CENTCOM on Task Force Scorpion Strike gives important technical information: LUCAS drones were used as a one-way attack squadron, cost about $35,000 each, were designed to work on their own, and could be launched from catapults, rockets, and mobile systems.
From a campaign-design perspective, one-way drones add three educational effects:
- Inventory pressure: defenders may spend expensive interceptors against cheap attackers.
- Sensor/decision overload: multiple inbound tracks stress radars, C2, and engagement timelines.
- Shaping and deception: drones can act as decoys, forcing radars on, revealing emitter locations for EW/SEAD targeting.
None of this requires the drones to be “perfect.” Their value often lies in forcing the defense to react, which exposes it.
3) Force Protection: Epic Fury’s Constraint
A raid can be “clean” in the air but still be dangerous later. This is clear right away in Epic Fury. The AP reports that Iranian retaliation in Kuwait resulted in the deaths of three U.S. soldiers and the serious injuries of five others. Other soldiers sustained minor injuries.
The Washington Post adds a key technical issue: defending a large area against a mix of threats (ballistic missiles, cruise missiles, and drones) can put a lot of stress on layered air defenses, especially since intercepting raids may need more than one defensive missile for each threat.
Lesson learned: in modern regional wars, having “air superiority over Iran” doesn’t always mean “base safety in the Gulf.” The campaign’s chances of success are limited by the number of interceptor stockpiles, the range of radar coverage, the amount of warning time, and the number of sites that need to be protected.
4) Shift in Strategy: Raid to Campaign
Precision vs Verification
Midnight Hammer showed that it could hit HDBT aimpoints with surprise and scale, which was a believable ability. But the strategic question is still BDA: How much time was gained, and what resources, such as materials, spare centrifuges, and secret sites, managed to survive?
Endurance Beats the Network
Epic Fury’s signature is not just one weapon; it’s the combination of electronic warfare (EW), intelligence, surveillance, and reconnaissance (ISR), communications relay, tankers, standoff fires, and low-cost mass into a long-term kill chain. That orchestration comes with its own risks, like munitions catching fire, weaknesses in bases, and how long it takes and how many people die at home and abroad.
Conclusion
Epic Fury and Midnight Hammer use two different ways to force people to do things. Midnight Hammer used stealth, deception, and penetrators to solve a small HDBT problem, but verification was still up in the air. Epic Fury targets the larger military system by using speed, networking, and cheap mass. Endurance, force protection, and reconstitution speed are now the most important things.
References
- U.S. Central Command (CENTCOM)—U.S. Forces Launch Operation Epic Fury (Press Release, Feb 28, 2026).
- Reuters—The US bombing of Iran started with a fake-out (June 22, 2025).
- Defense News—US Air Force eyes improved comms with bombers after Midnight Hammer (Jan 30, 2026).
- Air & Space Forces Magazine—Weapons of “Epic Fury”: Fighters, Missiles, and “Special Capabilities” (Mar 1, 2026).